A professional analysis by Totus Technologies
For the past decade, the conversation around European data sovereignty has followed a predictable pattern. A crisis emerges, regulators promise action, and then, as tensions ease, the status quo quietly reasserts itself. But the current moment feels different. The convergence of long‑standing US legal frameworks, a shifting geopolitical landscape, and a new wave of EU regulation is transforming data sovereignty from a political talking point into an operational boardroom imperative.
The CLOUD Act’s Long Shadow
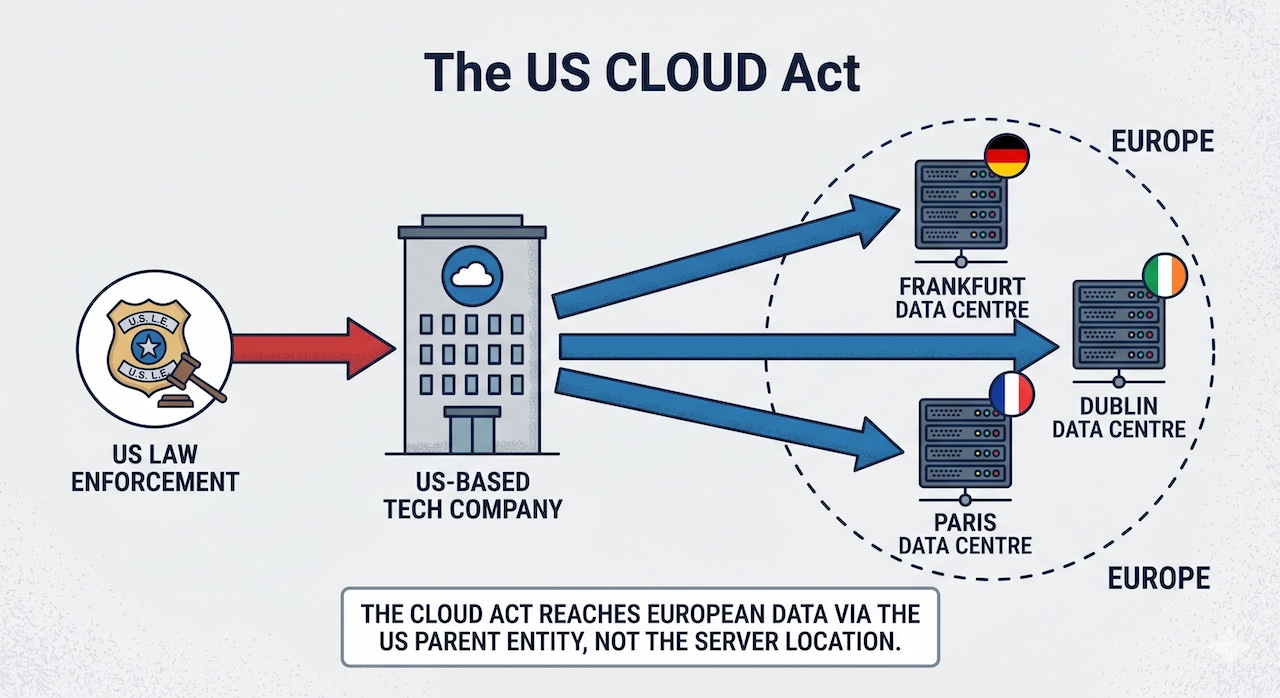
The 2018 US CLOUD Act (Clarifying Lawful Overseas Use of Data) remains the single most significant legal challenge to European data autonomy. It empowers US law enforcement to compel American‑headquartered technology companies to disclose data, regardless of where that data is physically stored.
Many European organisations mistakenly believed that storing data on European infrastructure—say, a Microsoft data centre in Frankfurt—offered protection. The CLOUD Act renders that assumption invalid. For any European enterprise using a US‑controlled platform (a category that includes not only hyperscale cloud providers but also ubiquitous SaaS tools), the legal jurisdiction governing that data is ultimately Washington, not Brussels or Berlin.
Geopolitical Tailwinds That Changed the Calculus
For years, this legal vulnerability was theoretical. The US was a trusted partner, and the risk of aggressive extraterritorial enforcement seemed remote. That perception has shifted, driven by a few key developments.
Regulatory Divergence Accelerates
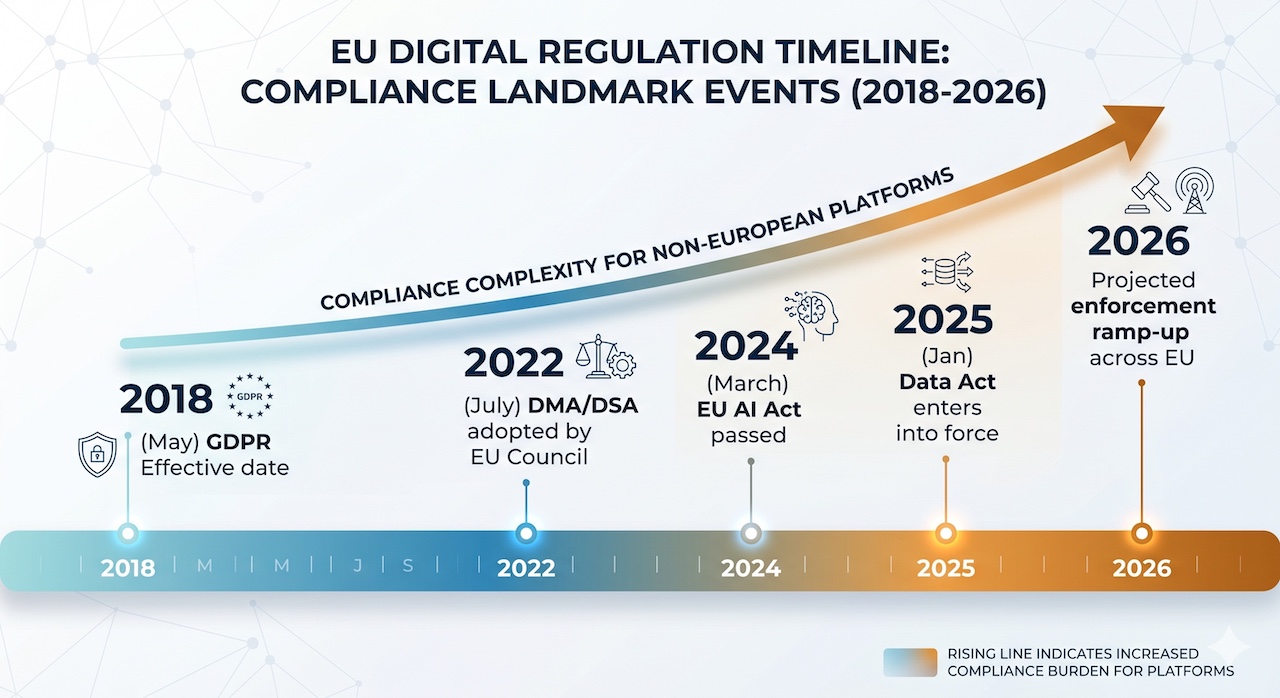
The EU has enacted a dense web of digital rules including the GDPR, the Data Act, the AI Act, and the Digital Markets Act (DMA). These frameworks prioritise data protection, localisation, and fundamental rights. They are increasingly incompatible with the US surveillance‑centric model embodied by the CLOUD Act.
Geopolitical Volatility Becomes a Boardroom Risk
The deterioration of transatlantic relations over the last 18 months has injected a new, unwelcome variable into risk assessments. The strategic dependence on US technology is no longer seen as a neutrality but as a potential point of leverage or vulnerability during diplomatic disputes.
Trust in US Tech Platforms Erodes
Beyond formal regulation, the perception of a deepening cultural and political divide between European values and the actions of some US tech leaders has made ‘sovereignty’ a more resonant selling point, even for purely commercial buyers.
The Operational Risks, Summarised
| Risk Category | Description | Example Scenario |
|---|---|---|
| Legal Conflict | Direct conflict between US disclosure demands (CLOUD Act) and EU data protection rules (GDPR). | A French hospital using a US cloud EMR is ordered by a US court to release patient data, violating GDPR. |
| Regulatory Sanction | EU regulators fine European organisations for using platforms that cannot guarantee data locality and protection. | A German automotive supplier faces a €20M GDPR fine for data transfers to a non‑compliant US‑parented CRM. |
| Geopolitical Exposure | Your critical data and operations become a potential bargaining chip in transatlantic disputes. | A manufacturing firm’s supply chain data is sought under a US sanction regime, freezing critical operations. |
| Reputational Damage | Public or client perception that your organisation cannot guarantee data safety from foreign legal reach. | A European bank loses a sovereign wealth fund mandate due to perceived US data exposure in its analytics stack. |
From “Cloud Washing” to “Sovereignty Washing”
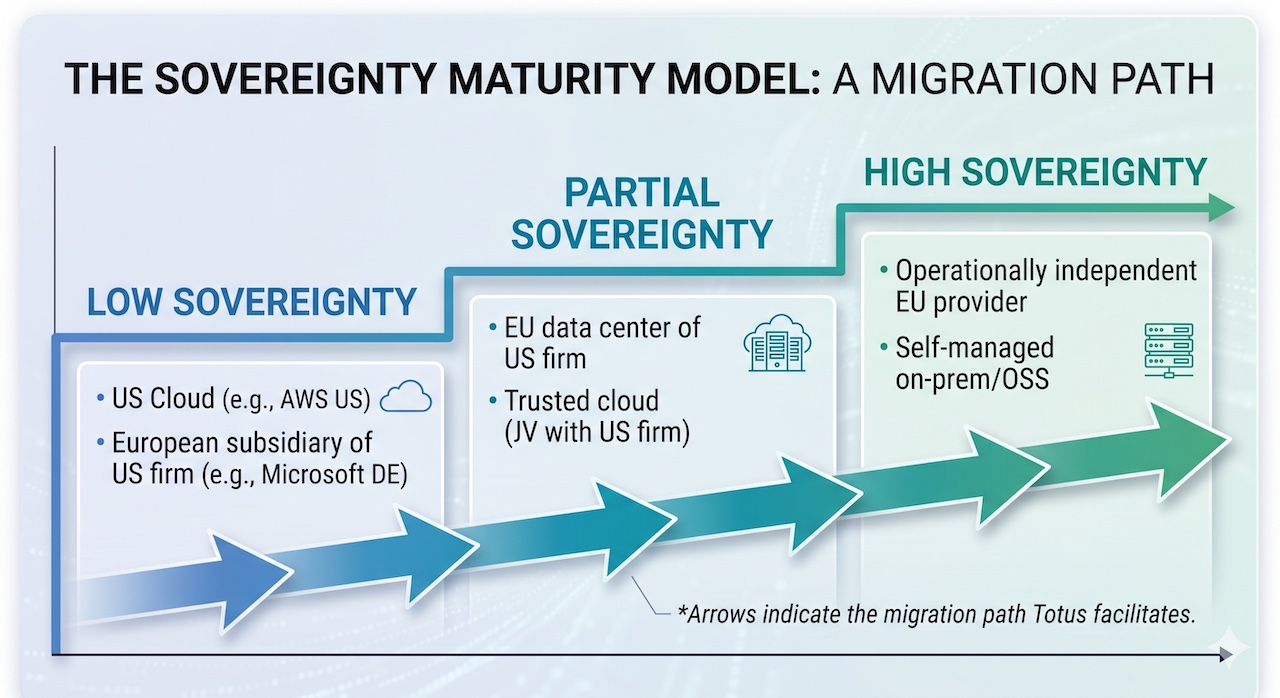
A note of caution: the market’s response has not always been transparent. We see a rise in what might be called ‘sovereignty washing’—solutions that claim European independence while retaining hidden dependencies on US infrastructure or legal entities.
Examples include so‑called “trusted clouds” that are joint ventures with a US hyperscaler, or European‑branded SaaS tools that store data on US‑controlled backend services. For a procurement officer, distinguishing genuine sovereignty from marketing requires a rigorous audit, not just a check of a company’s headquarters address.
A Professional Path Forward
Navigating this landscape does not require a wholesale rejection of American technology. Many US firms offer excellent products. The goal of data sovereignty is agency and optionality: the ability to choose, to control, and to change your mind without being exposed to legal or geopolitical risk.
At Totus Technologies, we believe the path to genuine sovereignty rests on three professional pillars:
- Discovery & Audit: You cannot secure what you do not know. A comprehensive audit maps every data flow, vendor dependency, and legal vulnerability across your entire technology estate.
- Structural Decoupling: Strategic migration away from platforms that create extraterritorial legal exposure. This often involves repatriating data to EU‑jurisdiction infrastructure, adopting auditable open source systems to eliminate vendor lock‑in, and building or procuring sovereign alternatives.
- Operational Autonomy: The final transfer of full ownership—including code, cryptographic keys, and operational control—to your internal teams. The external consultant’s success is measured by how quickly they become unnecessary.
The data sovereignty imperative is not about building a digital fortress around Europe. It is about ensuring that European organisations can compete, innovate, and serve their customers without their core digital infrastructure being subject to foreign legal veto. The geopolitical winds have turned this from a compliance exercise into a strategic necessity.
The question for European boards is no longer if they should address their digital dependencies, but how quickly and professionally they can do so.
This analysis was prepared by Totus Technologies. We help European organisations turn the ambition of digital sovereignty into a secure, operational reality. Visit our website or contact our team for a confidential, no‑obligation discovery audit.
#DataSovereignty #Geopolitics #CLOUDAct #DigitalIndependence #TotusTechnologies